COMODO Internet Security Premium Prevention Test/Review
3 posters
Page 1 of 1
 COMODO Internet Security Premium Prevention Test/Review
COMODO Internet Security Premium Prevention Test/Review
Just watched a rather interesting video of CIS. Several executables (clearly .exe file types) appeared to go right through Comodo's Defense+/Sandbox:
https://www.youtube.com/watch?v=h3_vFxPJ59I
I decided to test one of the executables myself (the first link that is tested in the video and that appears to bypass CIS). The file is called "exe.exe" and it is downloaded from a site that sounds like it hosts malware.
Instead of running it straight from Internet Explorer, I decide to download it on to my desktop. These are its properties:

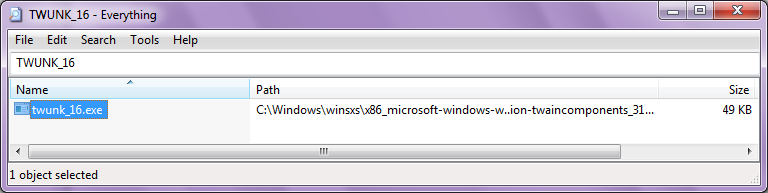
It actually looks like a genuine file and I've managed to Google it on other web-sites. Its original file name appears to be "Twunk_16.exe". Here's VirusTotal's analysis of it:


We can therefore probably conclude that this file is indeed harmless and not malware. I wonder if "ballader1" (the uploader of the youtube video) knows about this? I'd assume that the other files he tested and that bypassed Comodo were also harmless?
However, I don't really care about that really (the fact that "ballader1" is possibly/probably trying to maliciously make Comodo look bad - people do this all the time haha). What I really do care about is as follows:
1. "exe.exe" (a seemingly non-malicious file) seems to go right past CIS with no alerts. Even after unchecking "Trust applications digitally signed by Trusted Software Vendors", enabling Proactive configuration, and putting Defense+ at Paranoid level, no alerts are shown. Why is this?
2. The only alert Malware Defender shows is this:

For those that want to know, the complete "Cmd line" is:
3. Software Restriction Policies (SRP) blocks it:

So how does one explain this? I'm sure there's a perfectly valid (and obvious) explanation for this. Of course, this file doesn't appear to be malicious anyway, but I'm just confused at the fact that CIS didn't throw up any alerts and Malware Defender didn't reference the original file (while SRP did).
I'd appreciate any helpful comments. Cheers.
https://www.youtube.com/watch?v=h3_vFxPJ59I
I decided to test one of the executables myself (the first link that is tested in the video and that appears to bypass CIS). The file is called "exe.exe" and it is downloaded from a site that sounds like it hosts malware.
Instead of running it straight from Internet Explorer, I decide to download it on to my desktop. These are its properties:

It actually looks like a genuine file and I've managed to Google it on other web-sites. Its original file name appears to be "Twunk_16.exe". Here's VirusTotal's analysis of it:


We can therefore probably conclude that this file is indeed harmless and not malware. I wonder if "ballader1" (the uploader of the youtube video) knows about this? I'd assume that the other files he tested and that bypassed Comodo were also harmless?
However, I don't really care about that really (the fact that "ballader1" is possibly/probably trying to maliciously make Comodo look bad - people do this all the time haha). What I really do care about is as follows:
1. "exe.exe" (a seemingly non-malicious file) seems to go right past CIS with no alerts. Even after unchecking "Trust applications digitally signed by Trusted Software Vendors", enabling Proactive configuration, and putting Defense+ at Paranoid level, no alerts are shown. Why is this?
2. The only alert Malware Defender shows is this:

For those that want to know, the complete "Cmd line" is:
- Code:
"C:\WINDOWS\system32\ntvdm.exe" -f -i7 -w -a C:\WINDOWS\system32\krnl386.exe
3. Software Restriction Policies (SRP) blocks it:

So how does one explain this? I'm sure there's a perfectly valid (and obvious) explanation for this. Of course, this file doesn't appear to be malicious anyway, but I'm just confused at the fact that CIS didn't throw up any alerts and Malware Defender didn't reference the original file (while SRP did).
I'd appreciate any helpful comments. Cheers.
 Re: COMODO Internet Security Premium Prevention Test/Review
Re: COMODO Internet Security Premium Prevention Test/Review
Does "16-bit" have anything to do with it? I ask this because the process ("ntvdm.exe") that's called is described as follows:
http://www.liutilities.com/products/wintaskspro/processlibrary/ntvdm/
http://www.liutilities.com/products/wintaskspro/processlibrary/ntvdm/
ntvdm.exe is process that belongs to the Windows 16-bit Virtual Machine. It provides an environment for a 16-bit process to execute on a 32-bit platform. This program is important for the stable and secure running of your computer and should not be terminated.
 Re: COMODO Internet Security Premium Prevention Test/Review
Re: COMODO Internet Security Premium Prevention Test/Review
Its original file name appears to be "Twunk_16.exe"
It's the same windows file Twunk_16.exe. md5: F36A271706EDD23C94956AFB56981184
Sadeghi85- Member

- Posts : 66
Join date : 2010-07-22
 Re: COMODO Internet Security Premium Prevention Test/Review
Re: COMODO Internet Security Premium Prevention Test/Review
Does CIS use white-list?
Sadeghi85- Member

- Posts : 66
Join date : 2010-07-22
 Re: COMODO Internet Security Premium Prevention Test/Review
Re: COMODO Internet Security Premium Prevention Test/Review
Right, thanks Sadeghi85. That possibly explains everything. However, I still don't exactly understand why the Classical HIPS failed to give appropriate alerts. The fact is that a duplicate Windows file (renamed) came on to the desktop and was allowed to execute without any reference to it.
 Re: COMODO Internet Security Premium Prevention Test/Review
Re: COMODO Internet Security Premium Prevention Test/Review
Sadeghi85 wrote:Does CIS use white-list?
It's got a Classical HIPS, so not really. languy99 may be able to explain more.
EDIT: actually from memory, CIS does use a white-list, but I thought unchecking "Trust applications digitally signed by Trusted Software Vendors" would disable the white-list.
Sadeghi85- Member

- Posts : 66
Join date : 2010-07-22
 Re: COMODO Internet Security Premium Prevention Test/Review
Re: COMODO Internet Security Premium Prevention Test/Review
Sadeghi85 wrote:A post by yourself:
http://forums.comodo.com/news-announcements-feedback-cis/comodos-whitelist-database-t44245.0.html;msg320228#msg320228
Yes, I remember that thread. Essentially I still have no idea about this white-list and no one was able to clarify it for me in that thread (which was a little frustrating). Regardless, unchecking "Trust applications digitally signed by Trusted Software Vendors" would make this irrelevant right?
 Re: COMODO Internet Security Premium Prevention Test/Review
Re: COMODO Internet Security Premium Prevention Test/Review
ssj100 wrote:Sadeghi85 wrote:Does CIS use white-list?
It's got a Classical HIPS, so not really. languy99 may be able to explain more.
EDIT: actually from memory, CIS does use a white-list, but I thought unchecking "Trust applications digitally signed by Trusted Software Vendors" would disable the white-list.
the files he used in the test I bet were not all malware, files I use in my testing is verified malware. CIS does use a white list/trusted vendors list, remember that in 4.1 they are also introducing cloud white listing so even if you disable the trusted vendors list CIS sometimes still looks up the file on the servers and sees if it is safe allows it to run. The new version will really look everything up online.

languy99- Valued Member

- Posts : 54
Join date : 2010-07-20
 Re: COMODO Internet Security Premium Prevention Test/Review
Re: COMODO Internet Security Premium Prevention Test/Review
Thanks languy99.
I just went back to configure CIS so that it throws up an alert on everything "explorer.exe" does. It basically gives the same result as Malware Defender. So that part is solved at least.
However, I still don't understand why there is no alert asking whether to allow "explorer.exe" to execute "exe.exe". Of course, this is purely academic, but perhaps it's potentially a way for malware writers to exploit Classical HIPS in general?
I just went back to configure CIS so that it throws up an alert on everything "explorer.exe" does. It basically gives the same result as Malware Defender. So that part is solved at least.
However, I still don't understand why there is no alert asking whether to allow "explorer.exe" to execute "exe.exe". Of course, this is purely academic, but perhaps it's potentially a way for malware writers to exploit Classical HIPS in general?
 Re: COMODO Internet Security Premium Prevention Test/Review
Re: COMODO Internet Security Premium Prevention Test/Review
Those alerts are not there in the stock configuration. Only if you change it to proactive configuration will you see those alerts. There really is no need anymore for those alerts since the sandbox has come into use.

languy99- Valued Member

- Posts : 54
Join date : 2010-07-20
 Similar topics
Similar topics» Browserscope security test
» COMODO as AE
» Comodo: No!! No!!
» Comodo bypassed (allegedly)
» Comodo Virtual Kiosk for CIS 6
» COMODO as AE
» Comodo: No!! No!!
» Comodo bypassed (allegedly)
» Comodo Virtual Kiosk for CIS 6
Page 1 of 1
Permissions in this forum:
You cannot reply to topics in this forum|
|
|
